Posted by Defence Teaming Centre on
Working in Australia’s defence industry is a long-term investment. There are numerous requirements companies must meet before they are even considered for Defence’s supply chain.
One such requirement is ‘Security.’ The defence industry in Australia is a highly competitive and strategic sector that provides essential products and services to support the country’s national security. Companies operating in the sector must meet strict security requirements to win defence work and contribute to building Australia’s sovereign capability.
Defence Industry Security Program
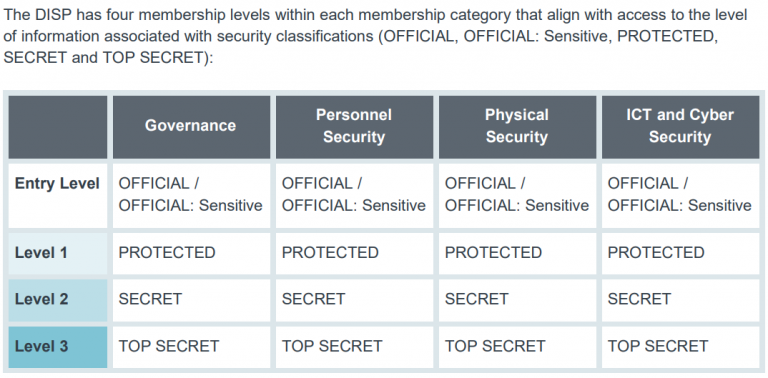
The Australian Government has a comprehensive security framework called the Defence Industry Security Program (DISP) to assist businesses wanting work in Australia’s defence industry. DISP was designed to ensure that companies working in the defence industry meet the necessary security requirements to protect sensitive information and assets. Subject to the types of work you undertake with Defence, DISP can be mandatory and the requirements can cover a range of security measures, including personnel security, physical security, information security, and cybersecurity.
One of the key reasons why companies need to meet DISP requirements is to protect our national security. Companies that work in the defence industry have access to sensitive information and technologies that could be used by foreign entities to harm Australia’s interests. To protect this information, companies must conduct background checks on personnel, implement physical security measures, and ensure that information is protected through secure communication channels and cybersecurity protocols.
Meeting the DISP requirements helps to protect companies and the nations Intellectual Property, supporting the growth of a strong Australian sovereign capability. The Australian Government is committed to developing the country’s sovereign capability by supporting local companies to develop their capabilities and contribute to the defence industry’s growth. Companies that meet DISP requirements are better placed to win defence work, which provides them with opportunities to grow their business and develop their capabilities.
The Australian Industry Group (Ai Group) has published a report titled ‘Working Securely with Defence‘ which provides guidance for companies seeking to meet DISP requirements. The report outlines the key elements of DISP and provides practical advice on how companies can achieve compliance. The report emphasises the importance of engaging with the defence industry and building strong relationships with key stakeholders, including the Defence Security Authority (DSA) and DISP members.
Cyber Security
Cybersecurity is a critical aspect of defence industry security, and businesses operating in this sector must ensure they have robust cybersecurity measures in place to protect sensitive information and assets from cyber threats.
The threat of cyber-attacks is a growing concern for defence industry, with the potential to cause considerable damage to national security and the operations of companies working in this sector. Cyber-attacks can take various forms, including stealing sensitive information, disrupting operations, and sabotaging critical infrastructure.
To mitigate the risk of cyber-attacks, businesses in the defence industry must implement strong cybersecurity measures that meet the DISP requirements. This involves using secure communication channels, ensuring that information is encrypted, regularly updating software and systems, and conducting regular cybersecurity assessments and training for employees.
The Australian Government has recognised the importance of cybersecurity in the defence industry and has established the Australian Cyber Security Centre (ACSC) to provide guidance and support for businesses operating in this sector. The ACSC offers a range of services, including cybersecurity assessments, threat intelligence sharing, and incident response planning, to help businesses identify and respond to cyber threats effectively.
In addition to meeting DISP requirements, defence industry businesses must stay up to date with the latest cybersecurity trends and threats. This involves keeping abreast of emerging technologies, sharing threat intelligence with industry peers, and investing in cybersecurity research and development.
What is the Defence Teaming Centre doing?
In June 2022, the Defence Teaming Centre (DTC), in conjunction with Saab Australia and BAE Systems Australia released the Cyber Frame for the Defence Industry (CFDI) to measure and increase the cyber resilience of Small to Medium Enterprises (SMEs) wanting to work on Defence Projects.
CFDI does not replace DISP, instead it helps companies continually maintain, update and upgrade their security. The DTC highly encourage all companies to complete the CFDI on an annual basis to help find areas that could/should be improved.
More recently the DTC has been advocating to government to improve the processing times of security clearances, simplify the security clearance process for people moving to Australia from the US or one of the Five Power Defence Nations and negotiate with the US about their ITAR (International Traffic In Arms Regulations) requirements and the AUKUS Program to provide greater opportunities for Australian SMEs to be part of the international AUKUS supply chain.
In conclusion, businesses operating in defence industry must ensure they have robust cybersecurity measures in place to protect against the growing threat of cyber-attacks. Meeting DISP requirements is essential to ensure that sensitive information and assets are safeguarded, but businesses must also stay up to date with the latest cybersecurity trends and threats to protect against emerging risks. Businesses can build their resilience and contribute to Australia’s national security objectives by taking a proactive approach to security.